Using the default VMware vCenter server certificate in XenDesktop POCs - Cannot connect to vcenter server error
Website Visitors:One of the core tasks when setting up XenDesktop is to integrate it with the existing customer infrastructure, such as the virtualization platform. Following you can find a screenshot of the respective wizard:
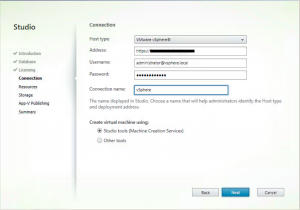
When integrating XenDesktop with vSphere or vCenter respectively, you might encounter the following error message:
„Cannot connect to the vCenter server due to a certificate error. Make sure that the appropriate certificates are installed on the vCenter server, and install the appropriate certificates on the same machine that contains all instances of the host service.“

As the error message indicates, XenDesktop is not able to connect to vCenter because it does not trust the server certificate in use. That commonly happens in POC environments where the customer has not replaced the self-signed server certificate, which is added to the vCenter server during installation, with a certificate signed by a trusted internal/external CA.
According to the XenDesktop Admin Guide in Citrix eDocs (http://support.citrix.com/proddocs/topic/xendesktop-7/cds-vmware-rho.html) a simple solution to this challenge is to connect to vCenter using IE, accept the security warning, click on the certificate warning and install the server certificate on the XenDesktop Broker. Unfortunately this does not work in all cases. But luckily there is another option to make it work:
Process for vCenter server 6:
Open firefox and enter https://vcenterserverFQDN. It will prompt for certificate error. If you open your vcenter server fqdn with IE and chrome, they don’t open it. Only firefox allowed me to do so. Create an exception. Once you do, it will open your vcenter server address.
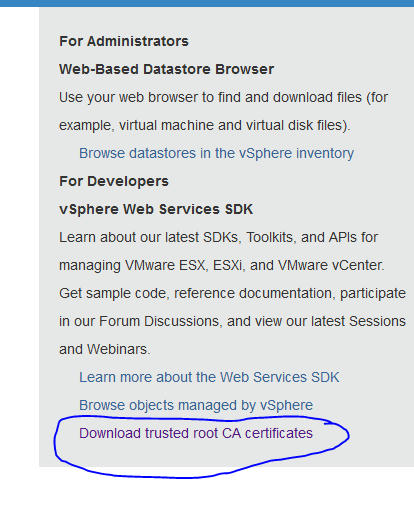
Click “Download trusted root CA certificates” as shown below:
Now follow below process:
- You would see a file downloaded with no extension.
- Using 7 zip software, extract contents of that file to a new folder.
- Open that folder. You will see a folder called certs. In that folder, you will have two files, rename the one which ends with extension as .0. Example, 4c5542a87.0. Now, rename it to 4c5542a87.cert.
- Double click it after renaming it. Choose local machine in next step and choose place all certificates in following store, and then browse and select trusted root certification authorities option. Hit ok and finish in next step.
In any web browser, open https://vcenterservernameFQDN and check if you still get certificate errors.
Below steps are useful when you have your delivery controller on 2008 r2, or 2012 or vsphere 5 or 5.5.
vCenter / vSphere 5.5
1. Connect to your vCenter server and browse to „C:\ProgramData\VMware\VMware VirtualCenter\SSL“
2. Copy the cacert.pem file to your XenDesktop Broker (to the C:\Temp directory for example)
3. Open a Microsoft Management Console (by running the mmc.exe command) as an Administrator
4. Add the Certificates Snap-In and choose “computer account” at manage certificates page, and then local computer account in the next page.
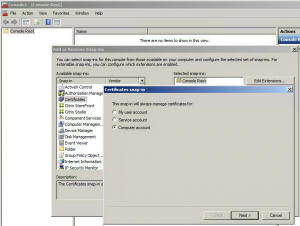
5. Browse to „Trusted Root Certification Authorities“ and select Import

6. If you follow the document link I gave above, you will already have a vcenter certificate file exported to your machine . Now Import it into (You need to select „All Files“ from the dropdown menu in the lower right hand corner, to be able to see it)
7. Now you should be able to see the vCenter certificate in the list of trusted certificates and XenDesktop should connect to vCenter without any error message.
Obviously there are good reasons for not using self-signed certificates in production environments, so you should use the aforementioned technique for POC environments only. For all other cases go and get a proper server certificate.
Posted in Citrix Blogs
More information here on xenapp and xendesktop 7.6 + , preparing master image steps. Check out the latest link below(Obtain and import a certificate column in below link):
Want to learn more on Citrix Automations and solutions???
Subscribe to get our latest content by email.