You have not chosen to trust "Symantec Class 3 Secure Server CA - G4", the issuer of the server's security certificate.
Website Visitors:Steps to resolve certificate issue in Macbook
(1) Log in to a Windows installation and use Internet Explorer to browse to the Citrix connection URL. This will force your Windows system to evaluate the SSL certificate chain used by the site and install any missing intermediate certificates into the Windows certificate store.
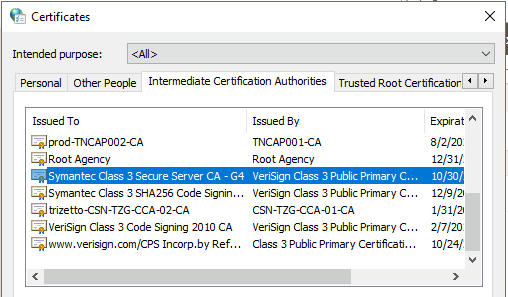
(2) Open Internet Options from Internet Explorer and got to the “Content” tab and click “Certificates”, select the “Intermediate certification Authorities” tab in the following dialog window. Look for the intermediate certificate Citrix Receiver is complaining about (in my case it was “Symantec class 3 secure server CA - G4”). Highlight and export the certificate (just use the default settings in the export wizard).
(3) Copy the certificate file to your Mac and double-click it. Keychain Access will open to install the certificate (also here stick with the defaults) enter your password if your Mac asks you for access to the system keychain.
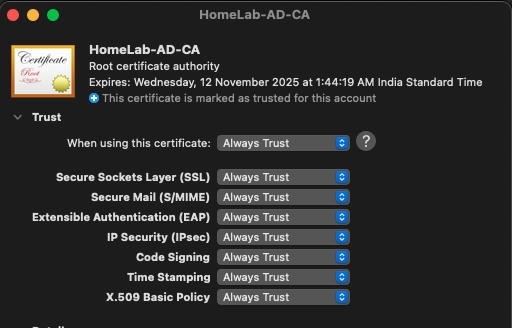
(4) In the keychain access app, to the top left, under Default keychains, click login and have a look at the certificate that you just added. If it is in red cross mark, double-click on that certificate, and select always trust option as shown below.
Open the citrix url. You should not see any certificate errors now. Unfortunately, you have to repeat this process for every failing certificate chain.
Similar issue with a different solution
Scenario: You have updated your Netscaler gateway URL’s certificate. You got your intermediate, root, and server certificate files given by your network/AD team. After installing the certificates on Netscaler, when users try to login to the Netscaler gateway and click on the app, users will get the error “you have not chosen to trust.. ca”. You can login to the Netscaler gateway successfully and see the applications. This means, Netscaler worked fine, and storefront enumeration is also successful. Ica file will also be downloaded. When you click on the ICA file, you will get the error.
You are already logged in to the Netscaler gateway URL. storefront already did the enumeration. ICA file is also downloaded, which means the storefront has no issues. Next either DDC, SF or app servers.
If you have HTTPS (SSL certificate) installed on your DDC, Install the new intermediate certificate and root certificate on the DDC and storefront servers.
Solution that worked for me
The solution that worked for me in this issue is, in the netscaler, I have linked the server certificate with intermediate certificate and intermediate cert with root certificate.
Imagine you are updating a certificate on the netscaler as it is near to certificate expiry. After importing the new server certificate to Netscaler, when you select server certificate and use the “link” option, you will see intermediate certificate shown there already. Click on the link option/button. Netscaler doesn’t automatically link server cert with intermediate cert. It will show the intermediate cert thats it.
For any cert issues, use sslshopper website and enter your netscaler gateway url. It will tell you, ssl/tls/ all errors. ssllabs and SSL Certificate Checker - Diagnostic Tool | DigiCert.com are other similar sites to check ssl information.
Want to learn more on Citrix Automations and solutions???
Subscribe to get our latest content by email.